Information Security - How do I secure my device - USB flash drive or mobile harddisk - Students UU - Students UU

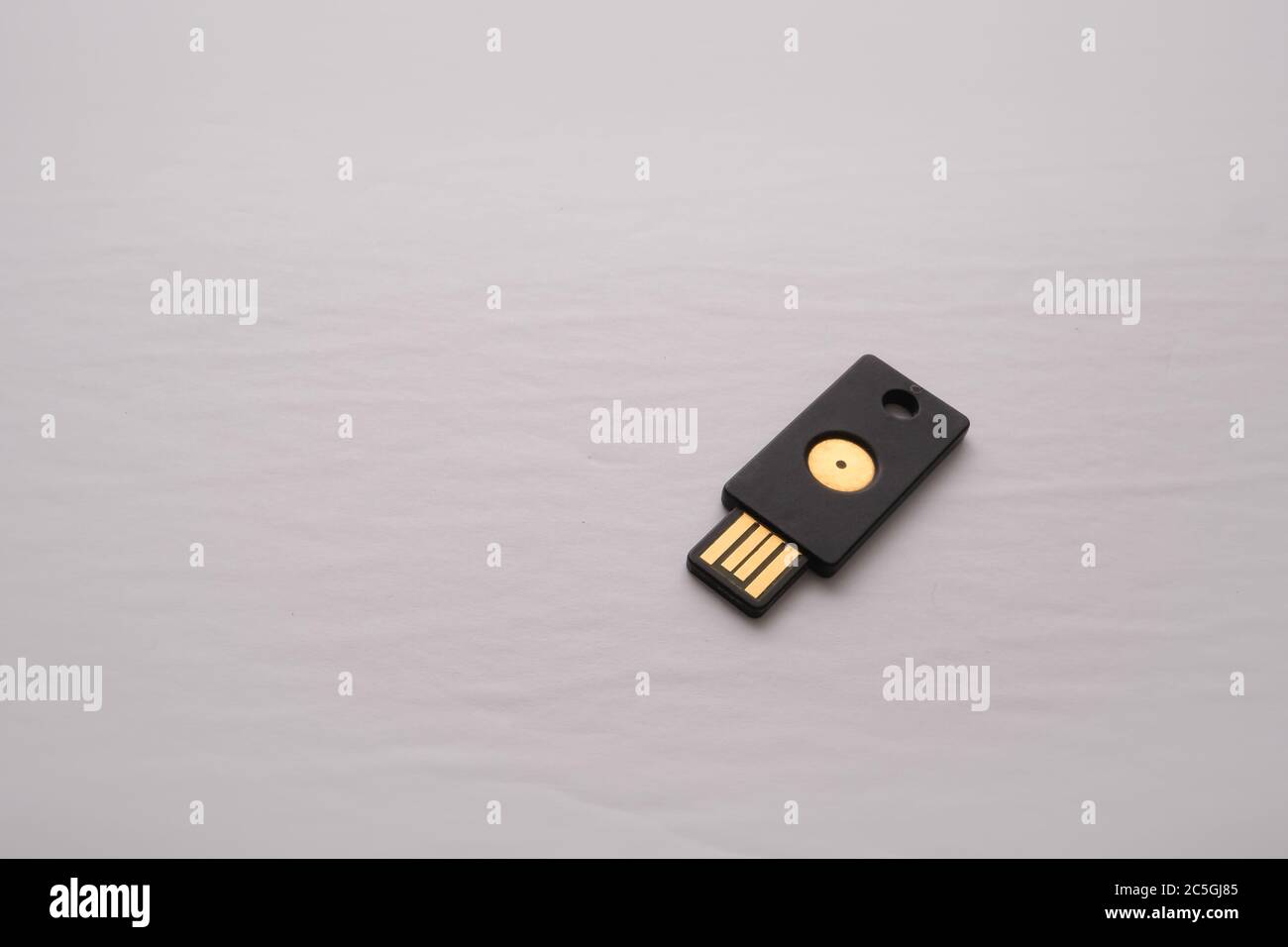
USB Security Keys: Everything You Need to Know - Logix Consulting Managed IT Support Services Seattle

8 Ports Usb To Usb Cables Laptop Burglar Alarm Display System Notebook Security Computer Mac Anti-theft Device For Retail Show - Alarm System Kits - AliExpress

SmartKeeper India - USB Cable Lock - Physical security device to prevent unauthorized removal of attached USB device. | Facebook